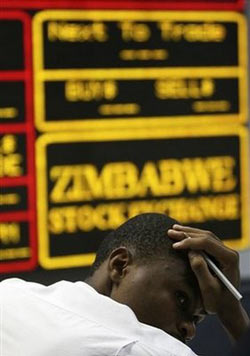
 We just got more information about the Zimbabwe Stock Exchange website hacking that happened 3 days ago. A source close to the issue says so far it has been established that the hacking happened at the application level of the website architecture. The nature of the hacking itself is not clear as the website has been shut down and the url (www.zse.co.zw) is redirecting to the hosting company’s website.
We just got more information about the Zimbabwe Stock Exchange website hacking that happened 3 days ago. A source close to the issue says so far it has been established that the hacking happened at the application level of the website architecture. The nature of the hacking itself is not clear as the website has been shut down and the url (www.zse.co.zw) is redirecting to the hosting company’s website.
On Thursday, the Zimbabwe Broadcasting Corporation reported that the ZSE website had been hacked. According to ZBC, a crisis meeting was held yesterday between the ZSE officials and the company’s consultants to find a solution to the problem.
The ZSE website was developed by a local company called Adept Solutions. The company provides Microsoft products’ training, Kaspersky Antivirus implementation, web hosting, email hosting and other IT related services. A problem at the application level of the website means there were vulnerabilities in the current implementation of the ZSE website.
The website itself is hosted by Webdev, one of Zimbabwe’s largest web development firms.

18 comments
Kabweza please, give us some technical soup, there is nothing which is in this story which l have not seen on other daily publications. lm very disappointed, l was waiting for this story to pop up on this site so that l can at get the technical side of events and this is what l get?
This site is on the rise and surely it will be there together with high techs like the theregister.co.uk, but a lot of groundwork needs to be done.
l had questions which l hope was gona be answered here like:
how did it happen, was it spear phishing?
was it social engineering?
who are the perpetrators, what are tracelogs showing, an outside IP?
what is the security setup like?
Do they have there own internal specialist or they are outsourcing?
who is going to take the blame, the ZSE or there hosting company?
what OS are they using, is it a customised or its the standard?
what was accessed and how much was taken?
And more………
@Macd, That may be releasing more sensitive operational type information in my opinion. MY hope would be: We hope the ZSE has security processes that ensure the site is secure and penetration test are done periodically to ensure vulnerabilities are not inherent in the codebase. We are reminded that we have to consider security as one of, if not, the integral part of any software we develop.
@Macd – as far as I know, they were using a custom PHP application. I
know this because I did a proof-of-concept a while back on scraping
share prices from the ZSE site. Hopefully they’ll include an API when
they redevelop the website, and join other stock exchanges in the 21st
century (one can hope).
@230385e3239bbfa9803f3a39b2294757:disqus the questions l have can be answered without revealing the technical details, hiding behind a blanket of secrecy will not help. This site is to provide information.
Yet another slop in basic security princiles. @ea25193fe8b994b12d8d7ce0e892a1b6:disqus
and others, the screen is clear here, ZSE hired a third party to develop their apps and no security architecture and design concepts were adopted resulting in substandard solutions being marshalled into the mainline network.
Also not that some of the questions you are asking may not be answered becoz the guys who broke into the site are professionals and there is no way they would leave their traces, moresore ZSE does not have any dynamic logging and monitoring capabilities such as Web Application firewalls, Security information Events Monitoring or IPS, so where do you think they will be able to scrouch the logs.
@Macd:disqus
, I am certain there was no form of social enginearing or spearphishing used here. Such tactics are only used if the targeted site is difficult to break. If there is so much security in place hackers resort to social engineering. This was not the case for ZSE, there is/was not basic security , an entriprisewide web app clogged with loopholes and vulnerabilities was in place and It was just like walking into a public toilet ..doors open for everyone type of scenerio.
From a security governance point of view, the ZSE senior management are responsible, and not Adept. They should put in place policies and procedures to ensure that Service providers don’t bring in such insecure crap into their environment.
The rise of Advance Persistent Threat(APTs) should change the culture of the big companies and they should start investing in reals security not the mumbling jumbling retoric staff they always say……
LOOOL WEBDEV!!!! has anyone even looked at their site. How often do you feel like puking when you look at such a messy website. Well I love it when people recognise the vulnerabilities of such old age implimented sites. Any scriot kiddy can take such a webiste down. In as much as I cant say much be assured more site are coming down.
I agee with macd, it would be nice (if anyone is willing to give out any info) as to how the attack was done, was it cross site scripting, sql injection, phishing scam etc?
Obviously exact details or logs should not be given to the public but it would be very interesting to know the method employed, it would also help other developers to learn about such loop holes.
kabweza – more like : BlackBerry blog hacked with riot-related threats
We know where you live, says hacking crew.
check – http://www.theregister.co.uk/2011/08/09/blackberry_blog_riot_hack/
This should be a wake-up call to those at ZSE, we live in a world of IT were secrecy can easily worsen your company or organization social and financial standing
@Macd and @504f6ea59b3d6ced7f3dc71b1d759565:disqus , every country is governed by disclosure laws. Take for example in the USA and other bigger economies there are laws which stipulate that if a company is breached or hacked it should disclose the impact of the breach and some further details(Governance laws). However, we don’t have anything like that in zim and hence ZSE are not oblidged to say anything. I am not saying they should but as for me I am more clear of what happened and the extent of the breach so whether they say it or not i understand what happened.
Having said that we need either some bodies , or powers that be within the business circles maybe the treassuries commission to put such disclosure laws in place. South Africa has something in their King 3 laws so why not zim.
I read that Zim is in the top 10 of the future hubs for IT in Africa. In as much as I am happy for that, I am a bit saddened by the culture of security which is lagging behind as other components of IT are slowly growing in zim.
It should be security first and the rest follows otherwise such hacks will alway occur and sooner or latter the big companies will be ashamed for not investing in security.
Finally , the attack did not use any form of social engineering or phishing it was a straight up bang on weekly coupled and poorly developed applications running on issecure backends and disoriented databases with open services and a lot of defaults enabled on top of unpatched OS, DBS and Apps…..
Also there are no logs to be shown to you guys becoz the ZSE does not do any logging and monitoring
when l first came across techzim started a while back, l sniffed around to see what was open and l have done it again today, l would like to say they have been a great improvement on the security side of this site!
Have l revealed anything? NO, thus what we want in Zim, a way of improving IT Security without hiding or fear of the unknown.
The hong kong stock exchange was also hacked
http://www.theregister.co.uk/2011/08/10/hong_kong_stock_exchange_hack/
And it’s still down as we speak…