After my previous article, the general consensus of those who commented on it was that running an email server would be too hard on a Startup. Now, I tend to disagree. While running an email server is not as easy as, say, taking care of your laptop and keeping it up to date, it is nowhere as difficult as some people are making it out to be.
I will be the first to say I am no expert. I however, have run and maintained several email servers ever since I set up a Postfix, Dovecot and fetchmail setup configuration back in Intrepid Ibex and that should count for something.
I have thus decided to provide my own email server recipe in a “I show you mine and you show me yours” gesture with the hope that it will help others out there including myself.
No one has managed to break into any of my email servers, of all these only one was blacklisted in CBL and even then it wasn’t really my fault. My email servers send a couple of thousand emails a day mostly newsletters send via MailPoet and a couple of personal emails.
I only check into my server once a week, unless there is some sort of problem which there is almost never is. During my check ups I look at the mail.log and the mail.err log files and the auth.log files.
I also perform updates and do a spam test on one of my newsletters using Mail-tester.com (I have been getting 10/10 for the past couple of months by the way). On average I spent about 30 minutes once a week on the email server and considering I would have to spent about $50/ month for the personal email accounts and $20 on an SMTP service like MailChimp or Amazon SES I consider it totally worth of my time.
A couple of problems were outlined in these comments to support the case that running your own email server is difficult including: downtime, spammers breaking into your server or using your domain name and your email being marked as Spam. I believe today’s article, as shown below, and the ones that will come in the series will solve all these problems.
My email server recipe
- The first thing that you need to do is to find a reliable server provider. Given things like ZESA issues and price I tend to favour foreign data centers as they are cheaper and have good uptime. I usually use: Amazon AWS, Dreamhost, SDAPP, Digitalocean and Oneprovider. These providers also provide DDOS protection (usually for free) which might come in handy once in a while when your server comes under a DDOS attack.
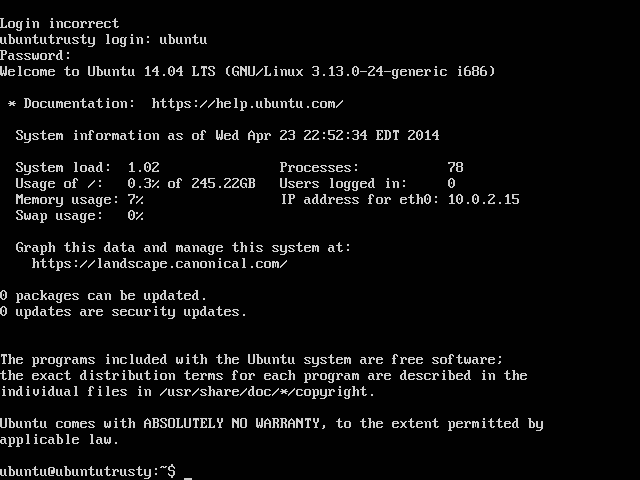
- Choose a distro you are most familiar with. I have always used Ubuntu and if this is your first time or if you are unsure you should too. To be fair configuring an Ubuntu server is no easier than configuring say a Debian, Redhat, Centos or Fedora server but Ubuntu is very popular and chances are whatever problem you have someone out there has already encountered and solved it. You should always choose the latest LTS version of Ubuntu which is currently 14.04.2. In all the steps below we will assume you have chosen Ubuntu.
- Once you have successfully installed your VPS, disable remote create a user with sudo privileges and disable remote root login. Follow the guide here.
- Switch from password login to certificate login using this guide.
- For a long time my auth.log log file was filled with ssh bots trying to break in. Changing your default sshd port as shown in this guide might help but the relentless crackers out there might do a port scan until they find the port and continue with their siege. I have come up with a custom solution of my own.
- My main email server is hosted by Dreamhost and like a lot other cloud providers they provide a panel where you can restrict the IP address or range that can access a certain port under security policies. Like most people I do not have a fixed IP address that I use to connect to the internet. My service provider has a NAT setup which means my IP addresses is constantly changing even if I keep my equipment on all the time. To get around this problem I went to ip-details.com and discovered my IP address which is was described as “ZOL 16E CUSTOMERS ON ALVARION PLATFORM”.
- I then did a search using the tcpiputils.com website to discover the entire CIDR block. Which I discovered is 197.211.192.0/18. I then restricted ssh access to this block. I have also restrict access to the IMAP port to this block since I only ever access my email using this same IP block. This wiped out all the attempts to the ssh port and reduced them to zero. If you are not sure you can just add all the Zimbabwean IP blocks. It is highly unlikely that there are some Zimbos out there looking to break into your email server.
- To further reinforce and guard against brute force attacks I installed fail2ban and configured it to ban repeat offenders for a year. So any attempts to break in via ssh or Postfix will be automatically thwarted. Remember to add you main IP block to the exception list.
- Before I cooked up the above solutions, I simply uninstalled sshd from my server! I instead used the provided browser based Qemu installation that my server provider provides.
- Once I have secured my server I install and configure Postfix. In my opinion, it is the easiest MTA server out there and the default installation would work for most. I usually use this guide. I prefer it to the default one here because it does not use “PAM” authentication thus precluding the need to create actual physical accounts on the machine and risk a break in, in the event that some user has a weak password.
- Setup Postfix to reject mail from invalid domains and domains that fail reverse lookups. Using the directive:
smtpd_helo_required = yes
smtpd_helo_restrictions = reject_invalid_hostname, reject_unknown_hostname - Reject mail from known spammers:
smtpd_recipient_restrictions =
reject_invalid_hostname,
reject_unknown_recipient_domain,
reject_unauth_pipelining,
permit_mynetworks,
permit_sasl_authenticated,
reject_unauth_destination,
reject_rbl_client multi.uribl.com,
reject_rbl_client dsn.rfc-ignorant.org,
reject_rbl_client dul.dnsbl.sorbs.net,
reject_rbl_client sbl-xbl.spamhaus.org,
reject_rbl_client bl.spamcop.net,
reject_rbl_client dnsbl.sorbs.net,
reject_rbl_client cbl.abuseat.org,
reject_rbl_client ix.dnsbl.manitu.net,
reject_rbl_client combined.rbl.msrbl.net,
reject_rbl_client rabl.nuclearelephant.com,
permit - Configure TLS using the guide I provided here.
- Have my service provider set up a reverse pointer record that matches my domain e.g. mail.myserver.co.zw.
- Setup a SPF record. We will look at how you can do this later on in the series.
- Setup DKIM signing and a DKIM record. We will also look at how you can do this later on in the series.
- Setup a DMARC record that expressly tells other smtp servers out there to reject all unsigned mail and all mail that does not come from your authorised mail server.
- Set up an alert at mailtoolbox.com for your domain to monitor possible blacklists on your IP and deal with them as soon as they occur.
- Have your users use a service like lastpass.com’s vault to generate and maintain strong passwords and change them regularly.
- Apply to the dnswl.org and tell them that you have done all the above and get on their whitelist.
- Set up an account at uptimerobot.com to monitor your server in and set up email alerts to your email account. Obviously this email cannot be on using the same domain name as the server so you can use your good old fashioned Gmail/Yahoo account.
- Check the Ubuntu CVE website here. Be sure to select the correct version of your Operating system. If there is nothing new it means there are no urgent updates on your server so you can update according to your preferred schedule.
- Check in at least once a week, read the server’s log files. I recommend using Atom.
NB One of the users made a remark about how Hotmail kept rejecting their email. This is probably because they have not set up the SPF,DKIM and DMARC records yet.
If you have and your email keeps getting rejected when you send it from Zimbabwe it is probably because you have not properly configured your email client. Usually this means your email client is sending mail directly and not via the MTA you have set up.
In fact if you have set up the three records above properly attempting to directly send email through your client should see it rejected by Gmail, Hotmail and most reputable servers because they would be following your directives not to accept such emails!
Another user cites possible misconfigurations and downtime as a reason for startups to avoid setting up their own email server. Well, if you choose reliable Data Centers such as the ones I have named above, downtime is something that will rarely happen if at all.
In any case most reputable MTA’s such as Postfix will defer sending email and attempt again thus largely negating any effects resulting from outages. As for misconfiguration causing problems, there are no really good reasons why one should mess with the above configuration once it’s set up.
If there is a reason for such changes they should be tested on another machine before being deployed into a productive environment and that is standard practice really.
I hope people find this useful and as always please feel free to comment and add to the article in the comment section.
13 comments
Garikai, another good way to protect SSH is to disable username logins, then use SSH keys rather. there are quite a few tutorials online on how to do this. all in all, nice article.
Thanks for the contribution and clarification. I had included it as item 5 on my checklist. Password login is something that should be avoided.
Hi Garikai,
Nice partial-rebuttal, but I remain unconvinced. I too am speaking from experience, and have the scars to prove it.
Hi Garikai,
(reposting, messed the formatting the first time)
Nice partial-rebuttal, but I remain unconvinced. I too am speaking from experience, and have the scars to prove it.
…to your knowledge 😉 Rootkits are notoriously hard to find, especially on servers you don’t own & can’t boot off a clean USB drive.
It’s never your fault when you get added to a blacklist – but it happens. I noticed you never mentioned how long it took for you to get off the blacklist (if you managed to get off the blacklist). Don’t you think startups might be averse to failing to deliver emails at random times for unknown lengths of time?
If you have the time, please address the other issues I raised:
*Do you backup your incoming emails? Do you have redundant backups in different data-centers with different providers? Do you have a Disaster Recovery plan that you test frequently. If you don’t test it, it’s worthless. How much time & money do you think a startup would spend setting up email backups?
* Do you have a warm fall-back mail server? What happens when you current one suddenly dies? Do you have automatic monitoring & automated switching to fall-back server? The mail server costs effectively double when you have a fall-back server running all the time
Email is absolutely critical for a startup: I don’t think you’d break a sweat if you lost yours for days at a time (I could be wrong), so you can afford to make it a ‘hobby’. To startups, I say concentrate on you Cow-Clicker app and leave email to email people who greet each other by ‘EHELO’. It’s takes too much time and money to do email right. You can afford to ‘wing it’ and don’t care too much about down-times or losing all your emails go right ahead.
I like you witty response. I have to concede email management is not for the faint hearted or those easily put off.
Hi, we use Whiteout.io clients which offer a 2GB plan for each user. That should cover most clients and their back ups. Dreamhost backs up their storage and also provide a $0.90/40GB which has a real time backup of the servers.
I don’t have a warm server but have a pristine snapshot of the one currently working. If for some reason it fails I can launch the snapshot in 5 secs! All backups will be restored on that server in about 2 mins automatically.
Another solution for startups would be to use Zoho for free for the usual accounts then set up an SMTP server for the hard work like sending out Newsletters. That would however require a little tweaking of the SPF record.
Also although it is possible, although very unlikely that someone breaks into your server, it would not take very long for you to discover this especially if they use the server for spamming since servers like Gmail, Yahoo and Hotmail send out daily dmarc reports showing the volume of email sent to them from your server. An unusual spike in email traffic to these will undoubtedly be revealed and the source can be investigated. There is no need for John the Accountant to send out 700 emails in one day.
I’m more inclined to agree with Tapiwa. As a startup better concentrate on the Cow-Clicker app than managing emails. For a small team of lets say 5-10 people, paying for Google Apps at $5 per user sounds like a great deal considering its mail and forget. Or go for my originally recommended Zoho Email which offers 10 accounts free of charge
I think these kinds of articles should be published frequently. They will determine how serious we call the Blog an IT News Platform. Even if you are not very technical in Email Server Management, but at least you can pick one or two just by doing a scheme reading. I havent learnt and confirmed something from this article. It has been written from a Zim perspective. My own experience is that I have been forced to do it because I have people who get employed and just spend time on facebook. So as the Top Manager I am forced to ensure that I personally attend to email issues otherwise I will hear unending stories.
I have subscribed to DNS Made Easy for Email Forwarding to my server. DNS Made Easy will be my MX 0 to 5 and my server will be the last. So all emails will go to DNS Made Easy. DME will check to see if my server is up(take care of ZESA and Poor ISPS). If its up I receive the emails. So not at any one moment have I lost my emails. I then change my SMTP port to Port 64000 (Not Real Port)..So DNS MadeEasy will use that port to deliver my emails. For send emails, I forward all emails to SpamWall which cleans all outbound emails because I have 35,000 users. Some of my users are phished and they release their password. So when Nigerians get hold of their credentials, they spam big time and my servers are then listed. I have solved this using SpamWall Cloud servers. They clean all emails from my side before they reach the public. The only problem I currently have is on backing up my emails because they come almost every millisecond. Does anyone have a solution for backing up highly transactional emails using Postfix.
my 2-step email server process:
1. Get Google Apps for Business
2. Get a beer
Seriously, this is crazy amount of effort for a commodity service in 2015
Kkkkk! Hilarious and I see you actually practice what you preach. I am guessing though one of the reasons for this is because the 500 email limit is not a problem for you because I cannot see an SES anywhere.
My thoughts exactly. I use GApps personally and love it. Fast and furious. But this is something I want to try for myself. Having signed up for the free 12 month AWS , I will give it a bash..
Is there a chance you could say all that in English Gari?
Phew…thats quite a lot work. Between setting up and running yo venture running the email server seems so much a handful I think its best to just hire from outside.
I would say stick to mailchimp for sending out mail to a list which I hace used in the past. u can also use mandrill.com(also from mailchimp) for sending transactional mail.
The costs are minimal and you can really focus on your venture
seriously, seriously – i can never recommend running your own mail server anymore – its just full of pitfalls and hurdles that risks your mail not getting to the intended recipient or worse no backups and losing all that data!
It’s far better and safer to let the people that do this for a living take care of this, I’m talking Office365, Google Apps, ZOL etc
for just outbound mail sending, Mandrill is free for up to 12k emails per month.
If your a startup why waste all that time (which is arguably more valuable than the $5 per month per mailbox that google apps costs) to setup/manage and maintain your own server?