Cyber security is a very hot topic the world over and has been a cause of concern the world over with companies big and small falling victim to a malicious attack known as RansomWare.
A local Cybersecurity firm, ProComm Group, says Zimbabwean companies have been the victim of RansomWare on numerous occasions.
Some companies have had their executive’s files encrypted by hackers who penetrate their companies’ networks. The hackers then demand payment (ransom), usually in BitCoin in order to release the files. Using BitCoin helps the criminals stay anonymous to an extent.
Procomm managing director, Tawengwa Toronga was speaking today at a Cybersecurity event organised by the company in partnership with CheckPoint one of the top global cybersecurity firms.
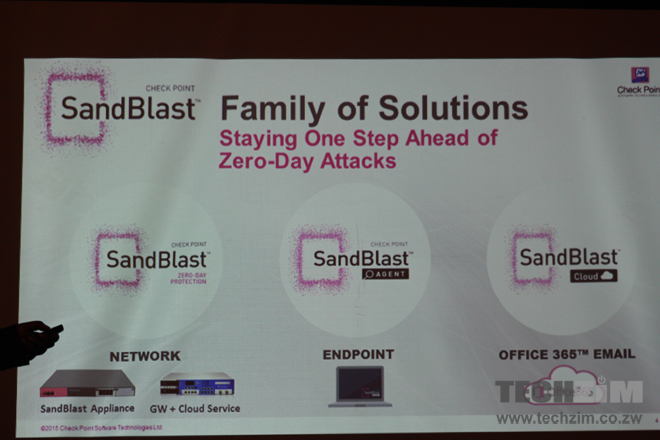
At the event, a Check Point security specialist Tau Mailula identified that most local companies are not protected from what are called Zero days attacks. Zero day attacks are attacks from virus and malware that are not yet registered in antivirus databases (new virus and malware).

Check Point and other companies like them have a process called Sand Boxing that protects enterprise networks and smartphones from such attacks.
Since this solution is mainly targeted at companies that communicate heavily via email, the Sand Boxing interception technique employed on this ransomware is performed through emulation. The emulation process goes as follows:
- Incoming email enters Sand Box system and any attached files are converted into pdf format before being forwarded to recipient.
- Original file is then emulated in Sand Box and if the attached original file is infected it is flagged and denied access to the network.
- If the original file is clean it is allowed into the network and made available for the recipient to download.
Other global companies that compete with CheckPoint include Cisco, Palo Alto and Fortinet.
Cyber security has emerged as one of the biggest threats in recent years because of the high internet penetration locally. Executives of large companies are particularly a target because they usually hold sensitive company data on their devices.

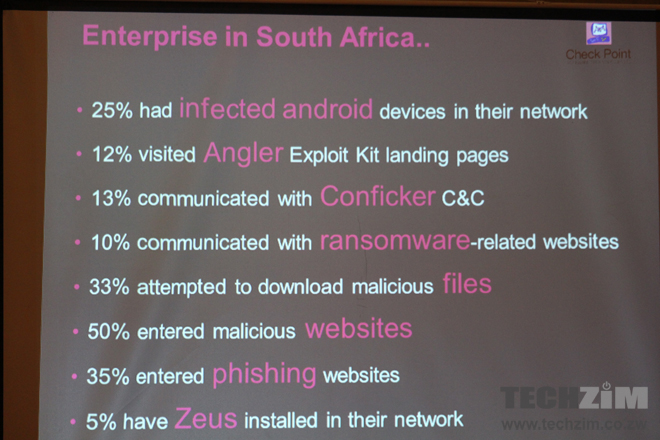
The event was attended by financial institutions, medical aid societies and government entities. A Check Point security expert at the event, Mailula said thousands of attacks are made on existing vulnerabilities on systems used by companies, from operating systems to applications.
Unfortunately the event was not attended by most telecommunication companies who enable the connectivity that creates access for cyber security attacks.

4 comments
“Some companies have had their executive’s files encrypted by hackers who penetrate their companies’ networks.”
umm no… thats not how it works….care to try again?
That is exactly how it works – the hacker does not need to be manually running port-scans to infect a network. Automated watering-hole attacks or a malware-laced web ads all count as penetrating a network and it is enough to gain an initial foothold. Spreading laterally within a domain is much easier. Automating the entire process increases the ROI of ransomware
so you are saying that malware/trojans are actually how they get onto the persons PC, rather than being penetrated via their network as implied?
Well it was NOT a cyber security event . It was more of an anti-virus event.
So it was proper for accountants to attend and not us.
Procomm wow they do everything from wireless , VoIP , IPBX , LAN , WAN , and of later Cyber Security interesting. They don’t know what they want.
****