In the past weeks, we have looked at the importance of information security in Zimbabwean organisations and the basics of InfoSec Governance. With such a background we can now diversify into one of the vital components of information security; building an effective enterprise security program.
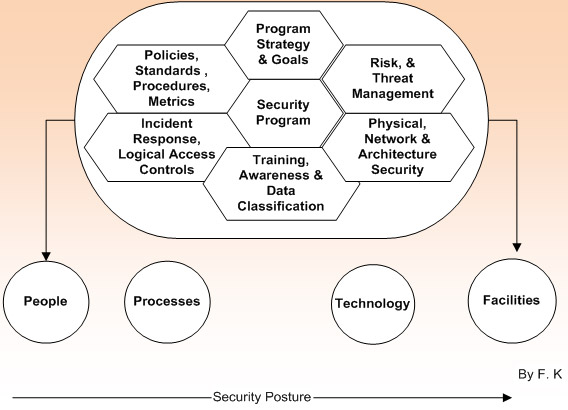
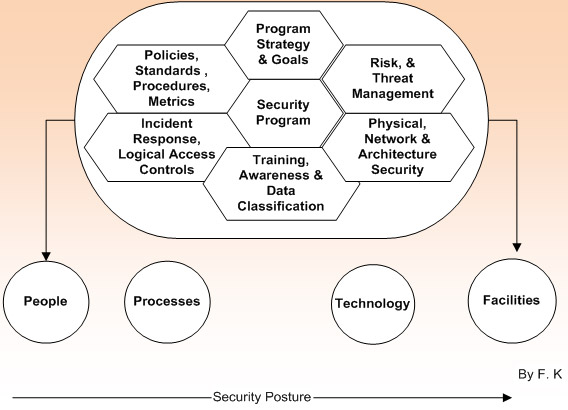
The information security program is a general framework made up of interlocking, interacting and overlapping blocks such as strategy, policies, standards, guidelines, procedures and architectural designs that drive the organisations security requirements inline with the organisations goals and strategy. It also brings structure and governance to the information security function within an organisation. This structure and governance allow the information security unit to function as a key element within the enterprise to support its business goals and decisions by providing information about the organisation’s information security capabilities in a business-friendly context.
Each organisation is different from another in terms of culture, goals and line of business. However, the elements that build a security framework are consistent across all business sectors. These elements are modular in nature, but depend upon one another for success. An effective information security program should include at least the following elements (Note: this is no an exhaustive list):
- Security Strategy goals and Program Governance
- Policies, Standards, Procedures, Guidelines and Principles
- Risk, Threat and Vulnerability Management program
- Security Roles and Responsibilities
 What’s in it for Zimbabwean Organisations?
What’s in it for Zimbabwean Organisations?
Implementing an effective information security program will bring about several benefits most of which we highlighted in the previous articles.
As a starting point of developing a program I would suggest that most organisations, business stakeholders and their ICT staff should follow the following generally accepted approach:
- Identify what they are trying to protect (Asset Inventory and Classification).
- Determine what they are trying to protect it from.
- Determine the likely risks and threats.
- Implement measures which will protect your assets in a cost-effective manner.
- Measure and review the process continuously and make improvements to the program
Developing a viable security program should not be a costly activity for most Zimbabwean organisations (looking at the current situation) especially that there are several frameworks that can be adopted as a baseline for building a security program. Some examples include ISO 27001, ISO 27002/05, SABSA, NIST etc. Organisations need to be careful when referring to these predefined frameworks though. These frameworks are based on organisations that already operate and effective security program. Therefore I would suggest that organisations should consider requirements that meet their business strategy and goals and leave out anything that does not fit or apply to their environment.
The main thing in it for Zim organisations is that they should have a security program in place or at least some of the basic building blocks to ensure that they are better protected from security threats, or data losses.
2 comments
whereas the Global environment is emphasising more on IT security due to what we can say “we are now operating in a global environment” ,i still believe that not much has been done to increase the awareness of Information Security in Zimbabwe.Most companies,including big corporations only realise weaknesses in their internal controls when something major has happened yet i do believe through what i have observed as an IT consultant that a lot of money is being lost through lack of IT Security controls.So the Question then comes “How many organizations out there really appreciate and understand the essence of IT security,How many even bother consulting IT Security experts to have their systems and procedures audited,What is really the mandate of such organizations as the CSZ in terms of increasing awareness and providing advice to companies”.Zimbabwe we need to work up and go Global.We have so many educated people but we just decide to be too ignorant.
Ben,
Your observations are true and the lack of Security in most organisations , Zimbabwean and world wide is costly.For the Zimbabwean case I would say its lack of Awareness and legislation. We do not have overarching bodies e.g. CSZ to foster Security policies locally for the various industries (Banking, Insurance, Health care etc), and under such circumstances the Board members are not even moved to act in any way. Maybe it needs a culture changes esp for those currently heading the zim companies or those in the IT industry. Sooner than latter we hope security will take its place esp that the economy is improving and that new initiatives of enhancing internet speed are underway.