 When looked at through the rose tinted glasses of time, sometimes the past appears to be more romantic that it actually was. For example one of the first Apple computers is expected to sale for over $500 000 and no the specs will not blow your mind: 8KB RAM and a 4 rows of A-D; I don’t eve know what that is. Why you could get more specs from a calculator but it is the history that people want. Apparently when it comes to computers some people are gutted that “they don’t make them like they used to.”
When looked at through the rose tinted glasses of time, sometimes the past appears to be more romantic that it actually was. For example one of the first Apple computers is expected to sale for over $500 000 and no the specs will not blow your mind: 8KB RAM and a 4 rows of A-D; I don’t eve know what that is. Why you could get more specs from a calculator but it is the history that people want. Apparently when it comes to computers some people are gutted that “they don’t make them like they used to.”
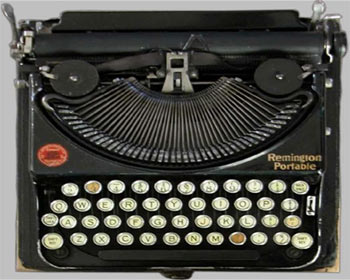
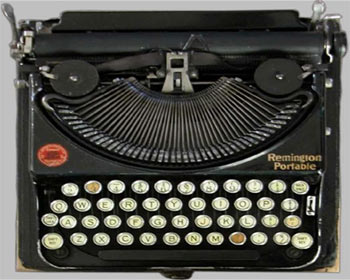
It seems however that some of the best spy agencies in the world are now trying to find their lost faith in old technologies like typewriters and polaroid cameras. In the wake of the NSA’s massive data mining project and revelations that some governments are hiring rogue programmers the Russians made an order for 20 typewriters. Allegedly this is so as to thwart PRISM and similar technologies. These are not one of those fancy models that you are sold in your local technology stores and have a USB no these are old school beasts.This has sparked talk on a new interesting strategy: going old school to secure your data.
Despite rumors by some that the Russians had been spooked into this, it seems the Russians government has always used typewriters. Perhaps this is why the Kremlin did not feature that much in the now infamous Wikileaks. Say what you will there is some logic to this. Back in the good old days of Kodak and polaroid cameras photography was an art. Journalists had to rely on their cameraman’s skills and nature rather than Photoshop for a good front page shot. Image manipulation was a rare and involved trade and the result was “what you saw was what you got.” Things were what they seemed.
Typewriters cannot be connected to a network connection that can be hacked or have its data intercepted nor can they be infected by some nasty virus or worm that can destroy all the data. To gain access to the data a thief has to gain physical access to it. This is beyond your hacker stereotype of a socially awkward hacker who lives in his parents basement. More likely the hacker will try another target that is more readily accessible.
For years people have speculated about the ownership and operation of the so called numbers stations. Mysterious amateur radio stations that broadcast a series of seemingly random numbers. One plausible legend says this is the work of intelligence agencies of unknown governments communicating with their field agents. They even made a movie about it.Despite all attempts no one has been able to break the code. In a spy world that is a good thing.
The fact that people have been able to break some of the most complex cryptographic ciphers when the lowly amateur radio has had the best of everyone is telling. Add the fact that shortwave radio stations are close to impossible to trace whilst modem technology like cell phones are beaming beacons then you have got yourself a winner.
Before you start running around town looking for museums and garage sales for old technology you should remember there is a reason why we ditched it. There will be new problems to contend with for example you will trade your fear of the hacker for the arsonist who can send your data up in smoke. Old tech is sometimes slow, difficult to operate, inefficient and can be a pain. Still you should really consider reliving the good old days, long before the Morris worm, for your most important data.
I am curious who would trade their tablet for a typewriter? Anyone?
4 comments
Why are computers that are supposed to be SECURE connected to the internet. Why would you connect a Nuclear Plant Server to the internet? I just don’t get it.
Connecting Nuclear Plant to the Internet? Which country is that? I know not of any
To quote the famous computer security truism:
The only truly secure computer is one buried in concrete, with the power turned off and the network cable cut (Anon)
Lol. I like this one!