Yesterday, POTRAZ, Zimbabwe’s telecoms regulator released a statement warning citizens to not abuse social media.
This has started discussions on whether or not the regulator has the capacity to monitor all social media and messaging platforms like WhatsApp.
While POTRAZ and the law enforcement agencies working on this are likely to have their own methods for identifying social media abusers, the remote monitoring of WhatsApp messages isn’t one of them.
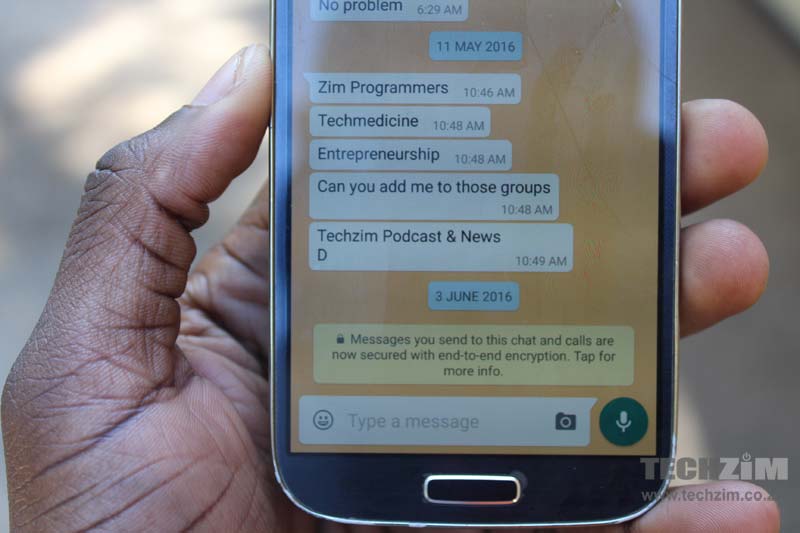
Three months ago, WhatsApp introduced End to End encryption (E2EE), a feature which secures all types of messages sent on the platform with a digital lock – meaning that only the sender and the receiver can open them.
Nobody else, including your internet service provider or your mobile network and even the team at WhatsApp, can access these messages.
Every WhatsApp user with a recent version of the app has the encryption feature, which also works for group messages and doesn’t need any special feature to enable it.
WhatsApp also made it easy for you to know whether the person you are communicating with has a version that’s E2EE enabled, via a notification specifically for that.
To be fair, though, As much as WhatsApp has added this type of technology to protect your privacy, it can only do this to a certain extent.
Your messages are only as private as the person or people you chat with. This reality of message privacy might inform how POTRAZ will identify social media abusers, but whatever the case, you can be sure that it won’t be via some unauthorised third party WhatsApp access.
15 comments
Beware of the screenshot
Can you tell us something about the SS7 Vulnerability
The SS7 vulnerability doesn’t affect WhatsApp per se, rather it’s an attack on the backbone of the mobile network. So technically speaking anything that you use your mobile phone to do will be affected if someone was to target your mobile number via this issue. Having said that the attacker would need to hijack your WhatsApp account, which they can try and do anyway without exploiting SS7 just by registering a separate acc, for them to have any messages destined for you to be delivered on their phone. So the attacker will not have compromised WhatsApp encryption, they’ll simply have hijacked your account in order to read the messages. WhatsApp employs security features that instantly asks any affected user to reverify their account if it detects the account has been registered on another device, leaving the attacker with a very very tiny window of opportunity to exploit this. Several conditions have to be in place too for a successful exploit, like the user must be asleep or away from their phone and you’d expect someone to try and send them a message in that same time. In reality this has a less than 1% chance of working. And you’d have to be some powerful person for anyone to want to launch an SS7 attack against you. To sum up, I can’t see any logic in trying to access your WhatsApp messages when someone uses the SS7 attack against you, they’ll be stupid to try and do that, the best will be for them to redirect your conventional calls and texts to their phone. That way they can monitor your communications without you ever knowing. But if they target your WhatsApp you’ll know it right away. That’s why I am adamant WhatsApp is the safest way of communicating in an environment like Zimbabwe. All other forms can be easily compromised without the user ever finding out.
can u guys add +27627151877 to Zim Programmes
Your title is grossly misleading and does not correspond to your content.
You will give people a false sense of safety instead of advising them well.
Key words are FOR LATEST VERSION ONLY!
If one of you is exposed with an old version, all of you are exposed through them.
Who the hell doesn’t have the latest version? Its free so why would everyone have the latest version?
i know a lot of people using some nokia and blackberry phones right now and those phones don’t support the E2EE encryption feature
Very important point..
Also to note cops need a warrant to sieze your phone also – saw this note via Dear ZRP facebook page that is probably relevant:
SEARCHING OF CELL PHONES BY ZRP …
Motorists are concerned about reports of ZRP searching cell phones at check points in Harare, and one contacted Senator David Coltart, who advises:
If this report is correct – namely that Police are demanding to have sight of cell phones at road blocks – then it is completely illegal. In particular section 57(d) of the Constitution states that “every person has the right to privacy, which includes the right not to have the privacy of their communications infringed”. There are a variety of other rights Zimbabweans have including the right of freedom of conscience and the right (in section 61(1)(b)) of “freedom to seek, receive and communicate ideas and other information”.
Whilst these rights obviously do not extend to propagating violence or hate speech the police have to have a reasonable suspicion that people are in fact propagating, for example, hate speech before they can seize cell phones. And before they can search they cannot do it on a whim and in any event need to obtain a search warrant from a court before doing so.
In all the circumstances citizens are entitled to refuse to hand over their cell phones to the Police. Any action by the Police forcing people to hand their cell phones over is illegal and unconstitutional.
Unquote.
THE ADVICE OF DEAR ZRP:
We don’t expect Dear ZRP… members to have content on their phones which might be offensive to the authorities, however this advice is given to reduce concerns of violation of privacy.
ZRP are aware that the search of cell phones without proper authority would be unconstitutional. Any ZRP personnel attempting to search a motorists’ cell phone without a court-issued search warrant, should have his authority confirmed. We advise motorists to contact a senior officer with details of the check point: location, name and rank and force number of the ZRP personnel, in order to obtain clarification.
The ZRP Contact List is available as download from the Files tab on this page.
The DEAR ZRP Team
Sure the messages are encrypted, what level of encryption you cannot say, this may serve to give users a false sense of security if the encryption level is too low and therefore easily ‘hackable’ – but the point of blocking whatsapp was to prevent messages circulating which would organise and communicate ‘unsavoury’ events.
The FBI cant hack Whatsapp now after they put in the encrytion, so there is no way in hell the Zimbabwean Police or CIO will be able to do it!
Hacking or not, how many msgs are sent and received per minute? Millions! This is big data we talking about. Who will be able to track all those millions of msgs unless they are only targeting specific individuals for which this encryption technology will work.
Erm, theoretically, it is possible to decrypt any message, you just need ginormous amounts of processing power and a keen mind. Never be complacent when it comes to tech security. Let us all admit that we lack the knowledge to know how it can be done, because we cannot discount the possibility of any messaging platform’s vulnerability.
Can I please be added into the Zim programmers book, my number is +358449557387
Attackers can exploit security holes in SS7 to track cell phone users’ movements and communications and eavesdrop on conversations. This attack is essentially a man-in-the-middle attack on cell phone communications that, among other things, exploits the lack of authentication in the communication protocols that run on top of SS7. (Remember SS7 is essentially used for setting up and managing the connection for a call, managing call forwarding, calling party name and number display, three-way calling, and other Intelligent Network (IN) services, etc)
Now to tear into a Whatsapp conversation you may need to use the following almost impossible mechanisms
i)Sniff into each single conversation (engage ISPs or MNO or Whatsapp Owners). In this option bear in mind you have to use a decryption algorithm way better than that used for encryption. This is almost impossible
ii)Hijack a session by directing all calls and messages to another number or masquerading as if you are the owner of the mobile number. In this option you may need to be reminded that whatsapp always verifies your mobile number each time you change. This option is not very useful because you only see what the user was supposed to receive and not what he was supposed to send.
In view of this , I think the best option for the government to see what subscribers are doing on Whatsapp is by physically accessing the cell phones.