Bulawayo-born programmer and drug lord Paul Le Roux is allegedly the brains behind TrueCrypt, an encryption application made famous by Edward Snowden.
In what reads like a script for a Hollywood action-thriller movie, the long form piece of investigative journalism chronicles Le Roux’s life from his birth in Bulawayo in 1972 , through his primary education in Mashava, and finally to his global criminal enterprise (by way of South Africa, Netherlands, US, UK and Australia). If you have 20 minutes to spare, I strongly urge you to read the whole article (which is episode 3 of a larger arc on him. If you have more than 20 minutes, read the earlier episodes on Le Roux).
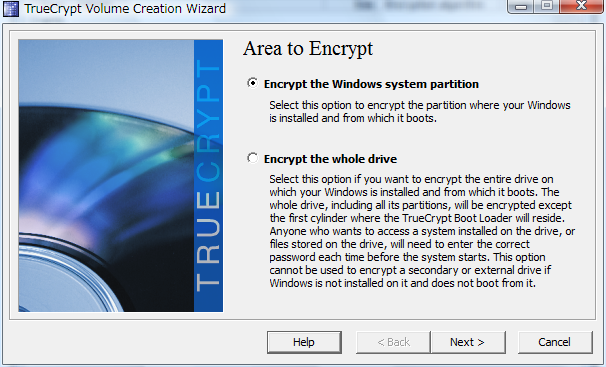
TrueCrypt is a cross-platform, Open Source application (since abandoned) that allows the encryption of individual files (or entire hard-drives). The NSA was unable to crack it, according to publicly available information. For years, no one knew the real identities of the anonymous group behind TrueCrypt (calling themselves “the TrueCrypt team”). TrueCrypt itself was based on a project that Paul Le Roux released under his name (Encryption for the Masses – shortened as E4M), until today, there were no known links between Le Roux and the TrueCrypt team.
Paul Le Roux is described as a brilliant programmer (self-taught).He has a long list of crimes attributed to him, including running an online pharmacy as well as ordering his enforcer – former US army sniper Joseph Hunter – to assassinate a Drug Enforcement Agency (DEA) agent.Unsurprisingly, Le Roux possessed legitimate passports as well as several fake identities including 2 Zimbabwean aliases (birth certificates and passports) as well as a diplomatic passport from the DRC that enabled him to evade searches when travelling internationally.
He was arrested by the DEA in 2012 in Liberia and turned informant before the airplane touched down on American soil has been cooperating with the US government since then. Incidentally, the “TrueCrypt team” made an announcement at the time of his arrest stating that the TrueCrypt should be considered as unsafe and declaring it as abandoned; commenters speculate that Paul Le Roux’s “TrueCrypt team” conspirators were pre-empting the possibility of the US government coercing Le Roux into releasing an intentionally weakened version of TrueCypt.
9 comments
Thanks for this find!
It triggered a lot of thinking behind the whole encryption saga….
What if truecrypt was discontinued to give way to a backdoored veracrypt??
Since he is now “working” with US(read nsa), maybe they hatched a plan to discard other mysterious truecrypt developers, then nsa got the help to build a “secure” replacement of truecrypt.
The mention of Tor specialist in the story got me suspicious. Lets not forget that Tor is a baby of NSA which they donated to opensource.
Tor’s secure privacy claims is not that clean to me considering that late last year a lot of tor websites were closed and people arrested in US, and to add salt to the privacy wound, FBI(NSA) boasted about having eyes everywhere even on encrypted internet traffic.
No to dismiss this, I am just wondering how difficult it is to introduce a (potentially permanent) backdoor in software that is developed in the open.
It is not difficult at all!
But the good thing about opensource is that the code that runs the software is open to anyone to inspect it and make recommendations. Security analysts, programmers everyone can tear the code apart and validate every bit of. So backdoors and and secret behaviours in the software can easily be identified.
Where my concern is is when weaker encryption is introduced that can be hammered by quantum computers. This computers are only in the hands of few organisations.
Another interesting read about Tor and FBI:
http://thehackernews.com/2016/03/fbi-tor-browser-exploit.html
I think it was MIT researchers that broke Tor.
It was a interesting read indeed. Discussion on this happening at https://news.ycombinator.com/item?id=11381625.
Brilliant, he may be, but being a criminal , not nice.
The lesson here is that if you really put your mind to it you can be truly evil. But in the end justice at least the U.S version eventually catches up with your
Only if it serves America interests. Ever heard of Project Paperclip, read it yourself from CIA website:
https://www.cia.gov/library/center-for-the-study-of-intelligence/csi-publications/csi-studies/studies/vol-58-no-3/operation-paperclip-the-secret-intelligence-program-to-bring-nazi-scientists-to-america.html