Could there be more to the broken ZPC website than we initially thought? Could the actual situation be much worse than a 404 error on a website? It’s possible. Let’s talk about it.
There is a gang of cybercriminals that call themselves the Everest Ransomware group. As the name suggests, they specialise in ransomware.
Everest’s ransomware is designed to encrypt files on the victim’s computer and then demand a ransom payment in exchange for the decryption key. The group also threatens to leak the victim’s data if the ransom is not paid.
In addition to ransomware attacks, Everest also engages in initial access brokering. This means that they sell access to compromised systems to other cybercriminals, who can then use the access to launch their own attacks.
The group has claimed to have compromised the systems of major organisations, such as AT&T, the largest provider of mobile telephone services in the United States. They have also claimed to have compromised NASA and other aerospace companies.
Closer to home, Everest claims to have hacked Eskom down in South Africa.
The same Everest group is now claiming that they attacked ZESA Holdings.
ZESA hacked?
ZESA Holdings
Today, the servers of the entire infrastructure of ZESA HOLDINGS (90% Country Electricity Manufacture) were attacked, including divisions ZETDC, ZENT, Powertel, ICS, IPMP, Smartvend, various oracle servers, big part of backups were also attacked.
Terabytes of internal (and interesting) data has been exfiltrated to our servers
- Internal financial data (Including WorldBank’s data and Indian Bank transactions and documents)
- Various system documents of partners, such as Indra(ES) and Inhemeter(CN)
- Employee’s Personal data
- Smartvendor customer data and previous customer personal data
The general managers of the company were re-notified about this situation. In order to restore systems and prevent the publication of data and subsequent damage, the person in charge should contact us using the instructions as soon as possible.
Apparently, Everest posted the above message on the dark web and it was picked up by some cybersecurity firms that have been following the activity of the group for years. I am not about to mess around on the dark web trying to verify that they made the claim and get myself on an Interpol watchlist.
We can trust that cybersecurity firms are telling the truth and then consider what that would mean. We have reached out to ZESA and will update you when we get a response.
Before we explore all this, do note that it may not be true. We mentioned above that Everest claims to have attacked AT&T in October 2022 but AT&T denied the claims. Do note though that many organisations pay these ransoms in secret to avoid reputational damage. AT&T could have paid.
What Everest is claiming
ZESA Holdings has a number of subsidiaries:
- Zimbabwe Power Company (ZPC) which is responsible for power generation
- Zimbabwe Electricity Transmission and Distribution Company (ZETDC) which distributes
- ZESA Enterprises (ZENT), their investment branch
- PowerTel Communications (Private) Limited, an internet provider
Everest claims to have attacked the servers of the holding company and its subsidiaries, except for the power generation unit, ZPC. They say they have copied all the data stored on those servers. In addition, they still retain access to the systems and may be holding some of it hostage too.
If true, they have access to sensitive data. There is the financial and employee data mentioned there.
If you couldn’t care less about the about, what about your data that is apparently part of the haul Everest has? If you are connected to the national grid or were once connected, Everest has data on you.
What can they do with it though, except damage the reputation of an organisation that has a terrible one to begin with? – you probably don’t care.
Unpacking the acronyms and unfamiliar terms
Regardless, here is what some of the other acronyms in their statement mean:
ICS – they are probably referring to the Industrial Control System. It is a type of computer system that is used to control industrial processes. ICSs are used in a variety of industries, including power generation.
Interesting fact – ICSs have been attacked by criminals and rival governments in recent years. The Stuxnet attack on Iran’s nuclear program and the Triton attack on the Ukrainian power grid are good examples.
IPMP stands for IP Network Multipathing. It is a feature in some operating systems that allows you to group multiple network interfaces into a single logical interface. This can be useful for improving network performance and reliability.
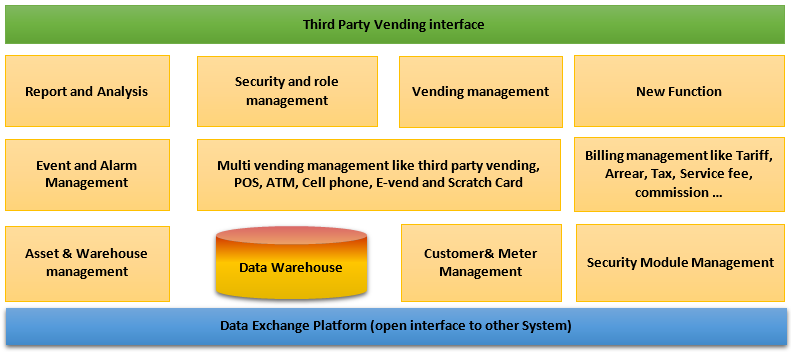
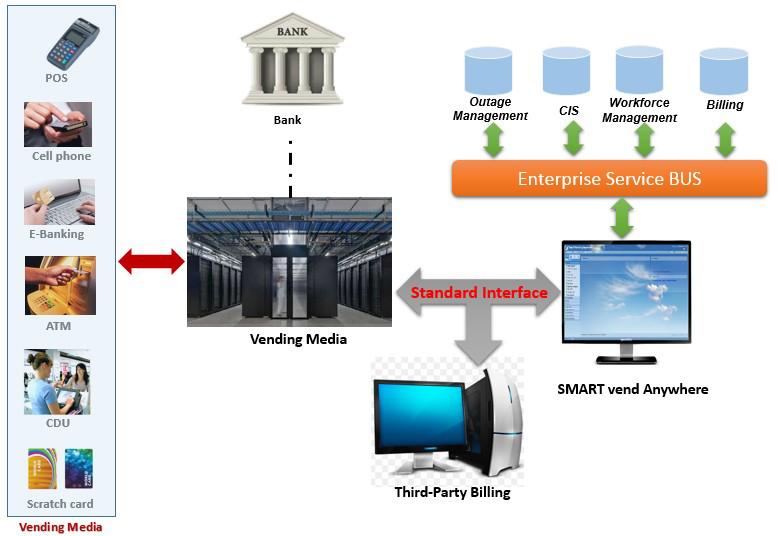
SmartVend is a web-based vending management system for utility companies. In other words, it is a prepayment electricity vending system.
Staying on SmartVend, this vending system is supplied by the Chinese company, Inhemeter. The Everest ransomware group claims to have the system documents of Inhemeter and other ZESA partners.
For those so inclined, here are the functions and system architecture of SmartVend
Not a new hack
This is not the first time we have heard about Everest hacking ZESA. It’s been a few years since we first heard of it. Hence why Everest says “The general managers of the company were re-notified about this situation.”
It appears ZESA has not paid up and so Everest is re-threatening them. Why would ZESA refuse to pay? There are a number of possible reasons:
- Everest is lying and ZESA has not been compromised
- ZESA has been hacked but believes there is little Everest can do to disrupt their operations. In other words, that they are mostly analog as to be invulnerable to cyber-attacks.
- ZESA does not have the money but is scrambling to pay
I’ll let the engineers school us on what could actually be going on here. The fact that Everest seems to have been struggling to get ZESA to pay makes for an interesting story.
I know many of you have a better idea of what’s going on here, do let us know in the comments section below.
Also read:
ZPC website that gives us electricity generation info is down, incompetence or something else?
Want to pay for ZESA using USD? Here’s all you need to know

What’s your take?